Digital Repository Software: How Far Have We Come? How Far Do We Have to Go?
Digital Repository Software: How Far Have We Come? How Far Do We Have to Go?
Bryan Brown’s tweet
led me to
Ruth Kitchin Tillman’s
Repository Ouroboros
post
about the treadmill of software development/deployment.
And wow do I have thoughts and feelings.
Ouroboros: an ancient symbol depicting a serpent or dragon eating its own tail. Or—in this context—constantly chasing what you can never have. Source:
Wikipedia
Let’s start with feelings.
I feel pain and misery in reading Ruth’s post.
As Bryan said in a subsequent tweet, I’ve been on both sides: a system maintainer watching much-needed features put off to major software updates (or rewrites) and the person participating in decisions to put off feature development in favor of major updates and rewrites.
It is a bit like a serpent chasing its tail (a reference to «Ouroboros» in Ruth’s post title)—as someone who just wants a workable, running system, it seems like a never-ending quest to get what my users need.
I think it will get better.
I offer as evidence the fact that almost all of us can assume network connectivity.
That certainly wasn’t always the case: routers used to break, file servers crash would under stress, network drivers go out of date at inopportune times.
Now we take network connectivity for granted—almost (
almost!
) as if it a utility as common as water and electricity.
We no longer have to chase our tail to assume those things.
When we make those assumptions, we push that technology down the stack and layer on new things.
Only after electricity is reliable can we layer on network connectivity.
With reliable network connectivity, we layer on—say—digital repositories.
Each layer goes through its own refinement process…getting better and better as it relies on the layers below it.
Are digital repositories as reliable as printed books?
No way!
Without electricity and network connectivity, we can’t have digital repositories but we can still use books.
Will there come a time when digital repositories are as reliable as electricity and network connectivity?
That sounds like a
Star Trek
world, but if history is our guide, I think the profession will get there.
(I’m not necessarily saying
I’ll
get there with it—such reliability is probably outside my professional lifetime.)
So, yeah, I feel pain and misery in Ruth’s post about the achingly out-of-reach nature of repository software that can be pushed down the stack…that can be assumed to exist with all of the capabilities that our users need.
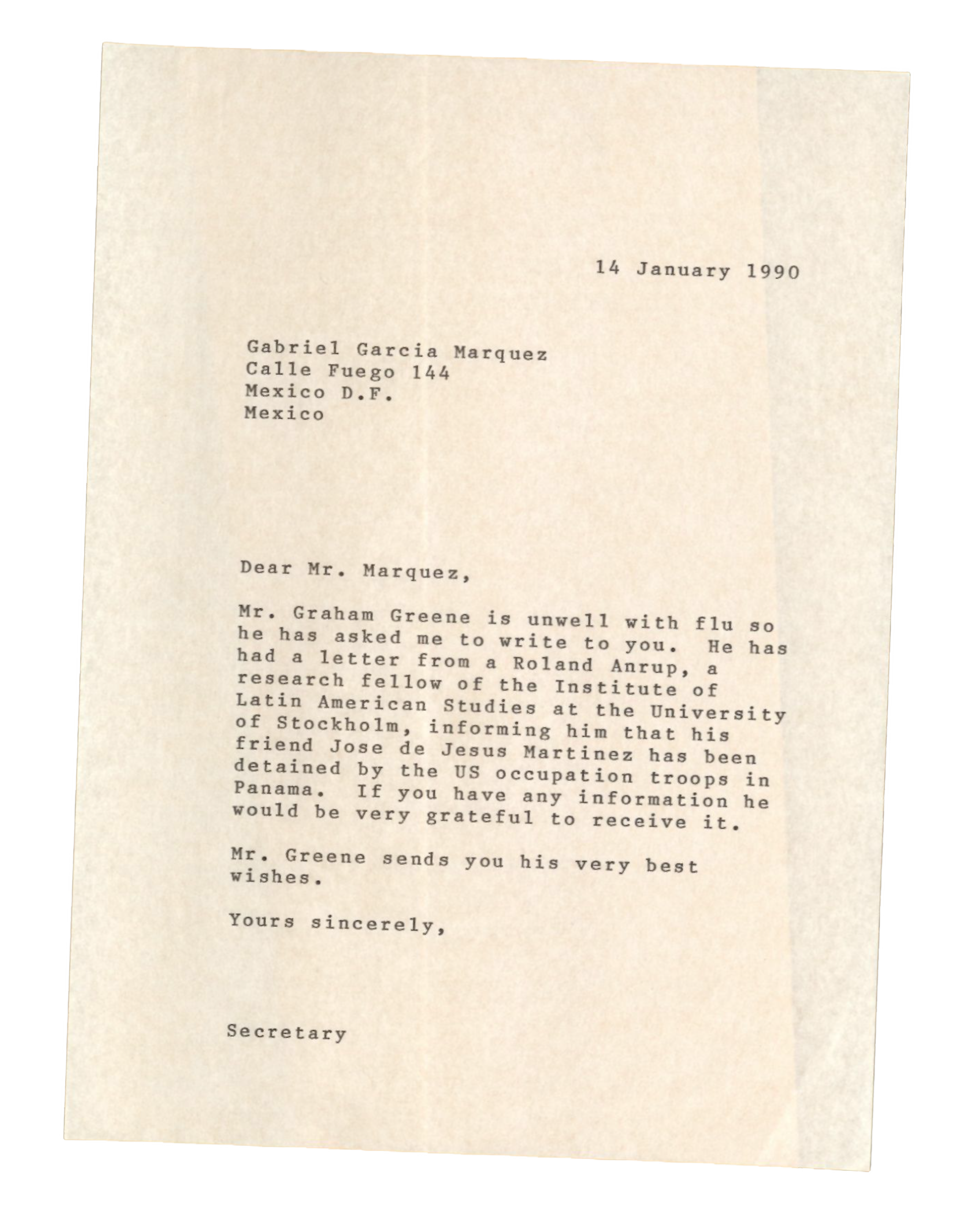
That brings me around to one of Bryan’s tweets:
If the idea of a digital preservation platform is that it is purpose-built to preserve assets for a long period of time, then isn’t it an obvious design flaw to build it with an EOL in mind? If the system is no longer supported, then can it really be trusted for preservation?
— Bryan J. Brown (@bryjbrown)
June 22, 2021
Can digital repositories really be trusted in-and-of-themselves?
No.
(Not yet?)
That isn’t to say that steps aren’t bein…